Visibility into physical security devices is one of the most persistent operational challenges in enterprise security. It’s not a new problem – teams have been struggling with it for years – but solving it at scale turns out to be considerably harder than acknowledging it. According to SecuriThings’ 2026 Physical Security Trends Report , only 3% of enterprise security teams have full centralized visibility into device status, configuration, and health across their locations. The other 97% are operating with partial or limited oversight, relying on a combination of platform-specific tools, manual processes, and periodic exports that were never designed to scale.
The gap isn’t for lack of trying. Most enterprises already run capable platforms – video management systems, access control software (ACS), vendor-specific dashboards – that provide meaningful operational coverage within their respective domains. The problem is that these tools were built to manage events and access decisions, not to maintain continuous oversight of device health and compliance across a heterogeneous, multi-site estate. As our Trends Report found, 76% of security leaders cite limited automation for routine compliance tasks as a key gap in their current toolset, and 74% point to a lack of centralized visibility across devices and sites. The tools they are currently using just aren’t designed for this job.
Among all the device categories that fall into this gap, access control readers may be the most underappreciated. They are the physical endpoints that employees and visitors interact with every day – the devices they badge through to enter buildings, server rooms, and restricted areas. In most enterprise environments they number in the hundreds or thousands, spread across multiple sites. And yet, in almost every deployment we encounter, they sit almost entirely outside the managed device estate.
Why Readers Are Particularly Difficult to Monitor
Part of what makes readers so hard to monitor is a fundamental architectural reality: most access control readers are not IP-connected devices. Unlike cameras or panels, which communicate directly over the network, readers are analog or serial devices: they connect to an IP-based access control panel, which in turn communicates with the network and the ACS. This means there’s no direct path to a reader from a network monitoring tool. Any visibility into the reader has to come through the panel managing it, and that relationship between reader and parent controller is rarely surfaced in a way that’s operationally useful.
Your access control management system does know about readers in the sense that it manages the access decisions they enforce: who can enter, when, under what conditions. But knowing a reader exists and being able to monitor its operational status are different things. Getting a live inventory of every reader across a multi-site estate from an ACS requires manual exports or custom queries, and the result is a static snapshot rather than a continuous feed. There is no aggregated view that surfaces each reader alongside its parent panel and live connectivity status. The data is somewhere in the system, but the operational layer that would make it actionable has simply never existed for readers the way it has for IP devices.
This is not a criticism of ACS vendors. Access control systems are purpose-built for access control. The gap between what they do and what continuous device management requires has less to do with capability than with design intent – and it’s a gap that general IT management tools cannot easily fill either, because readers don’t sit on the network in the way that IT endpoints do.
What the Gap Costs in Practice
The most immediate operational cost is in incident triage. When a door stops working, the question is whether the fault is in the reader, the panel it’s connected to, or somewhere upstream on the network. Without a view that maps each reader to its parent controller and shows live status for both in one place, answering that question means cross-referencing systems and making phone calls – a triage process that can stretch from minutes to hours depending on how the ACS is configured and who has access to what.
No wonder then that our Trends Report also found that 97% of physical security teams say manual device management impacts their ability to focus on strategic risk, with most describing the effect as moderate but pervasive. Reader incidents are a significant contributor to that overhead.
The compliance picture is a slower-burning version of the same problem. Readers have model numbers, vendor classifications, and lifecycle status – but as compliance requirements around physical security infrastructure continue to tighten, auditors are increasingly asking for documented oversight of the full access control endpoint estate, not just the IP layer. Most security teams genuinely cannot produce that information without a significant manual effort. It’s not negligence; it’s a structural gap that no available tool has addressed well until now.
SecuriThings Closes the Gap With Reader Visibility
SecuriThings already manages the IP device layer (panels, cameras, servers, network infrastructure, etc.) across complex, multi-site physical security environments. Our new reader visibility capability extends that management to the non-IP layer, pulling from our existing deep integrations with leading Access Control Systems like Genetec Synergis, Lenel OnGuard, and C•CURE.
With this new capability, SecuriThings automatically discovers every reader connected to every panel in scope by querying the existing ACS integration – no manual configuration, no spreadsheets. Each reader surfaces in a dedicated view alongside its parent panel, with live connectivity status and EOL/EOS lifecycle data. Navigation between panel and reader is one click in either direction, which changes the shape of incident triage considerably: when a door goes down, you can see immediately whether the problem is in the reader or the controller behind it.
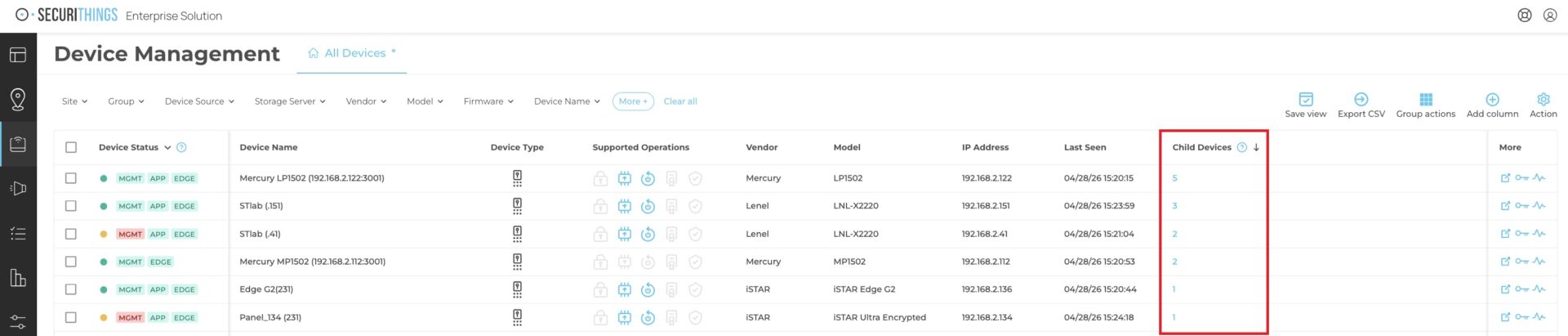
Highlighted: Readers (“Child Devices”) mapped to their respective panels inside the SecuriThings Platform.
That panel-to-reader association changes the shape of incident triage considerably. When a reader goes offline, the first question is always whether the problem is in the reader or the panel driving it. With both visible in a single view, that question is answered in seconds rather than through a multi-system investigation.

Pictured: Drilldown into individual readers inside the SecuriThings Platform
It’s worth being clear about what this represents in the broader context of what SecuriThings does. Visibility is the starting point, not the destination. The platform’s value has always been in enabling teams to act on what they see – remotely remediating issues, enforcing compliance policies, and managing device lifecycle – without the manual overhead or third-party dependencies that most teams currently rely on. Reader visibility brings that same operational model to a device category that has been unmanageable in any automated, scalable way until now.
Staying Ahead of the Curve
Reader visibility is also a reflection of something larger about where physical security management is heading. The compliance perimeter around physical security devices is expanding; our own Trends Report found that 75% of enterprise security leaders now rate device compliance as a high or top priority, yet 60% find maintaining that compliance either “moderately” or “highly” challenging. As that pressure grows, the gaps that teams have quietly accepted, including readers, become harder to justify. Meanwhile, OSDP adoption continues to accelerate, creating a more reliable path to richer reader data through panels over time.
In this context, the fact that 98% of security leaders are less than fully confident in their current tools to manage device health and compliance at scale is striking. These teams, particularly in enterprise organizations, are working with the best video management and access control systems; but they lack a layer of tooling purpose-built for continuous, automated oversight of the devices themselves, across every category, including the ones that don’t sit directly on the network. Readers are the most prominent example of that gap, and one of the most consequential to close.
With this new capability, SecuriThings closes that gap for physical security teams, surfacing every reader and its parent panel in a unified, continuously updated view that sits alongside the rest of the managed device estate.
You can’t protect what you can’t see. With SecuriThings, you can see all your physical security devices – and manage them in real time.





