Best Practices for Physical Security and Cybersecurity
- Chapter 1: Tutorial & Best Practices
- Chapter 2: Commercial Building Security Systems
- Chapter 3: Physical Security Systems
- Chapter 4: Data Center Physical Security
- Chapter 5: Physical Security Cybersecurity
- Chapter 6: Physical Security Plan
- Chapter 7: Physical Security Controls
- Chapter 8: Retail Security Systems
- Chapter 9: Physical Security Tools
- Chapter 10: Physical Security Program Best Practices
- Chapter 11: Physical Security Policy Best Practices
- Chapter 12: Best Practices for Physical Security and Cybersecurity
- Chapter 13: Best Practices for Corporate Physical Security
- Chapter 14: Physical Security Best Practices
- Chapter 15: How physical security powers
- Chapter 15: Best Practices for Physical Security Devices
- Chapter 16: Physical Security Assessment Best Practices
Physical and cybersecurity are no longer separate domains. As physical devices get connected to networks, critical systems blend digital and physical components, and a breach in one can rapidly affect the other. An attacker with physical access might disable cameras or plant rogue devices, while a cyber intrusion can manipulate building systems or unlock doors.
This convergence is evident in operational technology (OT) environments where industrial systems, access controls, and safety mechanisms are now connected to digital networks. While integration improves efficiency and visibility, it also expands the attack surface.
Real-world incidents—from ransomware shutting down hospitals to cyber-physical sabotage in manufacturing—highlight the growing need for unified security. As IoT adoption accelerates and remote automation becomes standard, organizations must rethink how they secure infrastructure.
This article explains how the physical and cyber domains intersect, identifies key exposure points to monitor, and outlines best practices that help build resilient, converged defenses.
Summary of key physical security and cybersecurity concepts
The table below summarizes the physical security and cybersecurity concepts explored in detail in this article.
| Concept | Description |
|---|---|
| The convergence of the physical and cyber domains | Modern infrastructure connects IT, OT, and physical systems, creating shared vulnerabilities. As boundaries dissolve, attackers can exploit one domain to access the other, and addressing this requires unified security strategies. |
| Exposure points in modern systems | Critical infrastructure faces vulnerabilities across the physical, cyber, and hybrid layers. Attackers exploit gaps such as unauthorized access, malware, insider threats, and cyber-physical pivot points, underscoring the need for full attack surface visibility. |
| Best practices for physical security and cybersecurity | A unified defense strategy encompasses layered protection, coordinated incident response, workforce training, continuous monitoring, and secure third-party management, all working together to mitigate risk across converged environments. |
| The future of physical security and cybersecurity | Emerging technologies like AI, IoT, and 5G will reshape the security landscape, requiring converged operations, intelligent automation, and adaptive defense models to address increasingly complex hybrid threats. |
-

Monitor the health of physical security devices and receive alerts in real-time
-

Automate firmware upgrades, password rotations & certificate management
-

Generate ad hoc and scheduled compliance reports
Understanding the convergence of the physical and cyber domains
Modern security challenges emerge from the convergence of three previously distinct domains: Information Technology (IT), Operational Technology (OT), and physical security. IT governs data systems, identity management, and networks. OT includes control systems like SCADA (Supervisory Control and Data Acquisition), PLCs (Programmable Logic Controllers), and DCS (Distributed Control System). Physical security safeguards people and facilities through access control, surveillance, and perimeter defenses.
Historically, these disciplines operated in silos. Today, digital and physical systems are deeply integrated. Access control doors connect to enterprise directories. PLCs send data to cloud analytics. Cameras stream over IP. As a result, every physical device becomes a cyber asset, and cyber incidents can trigger real-world consequences.

Convergence of IT, OT, and Physical Security. As digital and physical systems become increasingly interconnected, organizations face a unified threat surface where risks in one domain can impact the others.
This integration introduces complex risks. Legacy OT systems now coexist with IP-connected devices and wireless protocols, often without clear ownership. A badge reader failure could be routed to facilities, IT, or engineering. Standard tools may miss threats like logic manipulation or badge cloning.
Security policies must reflect this new reality by treating physical and cyber assets as part of the same ecosystem, with unified visibility, response, and accountability.
Exposure points in modern systems
Modern critical infrastructure operates within an expanded attack surface that spans physical perimeters, digital networks, and their intersections. As operational environments adopt connected systems, new exposure points emerge, often in places traditional security models fail to monitor.
Physical security remains a foundational layer of defense, even though unauthorized facility access continues to pose serious risks. Intruders gaining entry to control rooms, server cabinets, or equipment yards can bypass cyber protections entirely. Tampering with equipment, whether disabling safety interlocks or introducing rogue devices, can create conditions for sabotage or facilitate remote exploitation. Insider threats add further complexity; a trusted operator or contractor with physical access may leverage their position to install malicious hardware, extract credentials, or disrupt operations from within.
On the cyber front, common threats such as malware and ransomware now target not just IT endpoints but control systems and engineering workstations. Phishing and social engineering campaigns exploit human operators to gain initial access, while zero-day exploits allow attackers to infiltrate systems before patches are available. Remote access tools—critical for off-site monitoring and maintenance—introduce additional risk when poorly segmented or secured. A compromised VPN tunnel or shared credentials can become the gateway into core control environments.
The most dangerous exposure lies in hybrid attack vectors, where physical and cyber threats converge. Cyber-enabled physical sabotage occurs when attackers manipulate operational systems to cause real-world harm, such as altering pressure controls or disabling alarms. Conversely, physical breaches can be used to enable cyber compromise; for example, plugging an unauthorized device into a network port within a plant floor can provide persistent access. Advanced adversaries increasingly use blended tactics, simultaneously targeting physical failures and digital deception to delay detection and magnify impact.
Failure to map the true attack surface leaves critical gaps in defense. Security teams accustomed to focusing on isolated domains may miss the vulnerabilities that chain together, e.g., how a forced door, an exposed switch, or a compromised technician account can escalate into complete operational disruption. Understanding exposure points across the physical, cyber, and hybrid layers is essential to building resilient systems capable of withstanding modern threats.
Best practices for physical security and cybersecurity integration
Strengthening security in critical infrastructure requires a unified, layered approach that spans physical barriers, digital defenses, operational culture, and long-term resilience. Best practices cannot be segmented into departments or technologies; they must form an integrated architecture capable of anticipating disruption across both the physical and cyber domains.
Adopt a defense-in-depth approach (layered protection across domains)
Defense in depth remains the fundamental principle of integrated security. In physical environments, this means employing multiple layers of protection—such as perimeter fencing, controlled entry points, biometric verification, and intrusion detection—with each designed to delay and deter access.
On the cyber side, layered controls include network segmentation, identity access management, encryption, and application whitelisting. However, true modern defense extends further, combining both. Hybrid defense measures ensure that a single failure, whether it’s a forced door or a compromised password, does not provide full system access. For instance, a secure badge system with MFA tied to network identity merges physical presence with digital authentication, preventing adversaries from exploiting either domain in isolation.
The table below highlights the differences between converged defense strategies and conventional ones, and explains why they offer stronger resilience against today’s blended threats.
| Traditional security | Converged security |
|---|---|
| Physical and cyber protections are managed separately | Physical and cyber layers integrated through shared systems |
| Security relies on static perimeters and manual oversight | Security is continuous, data-driven, and automated |
| Incident response handled by separate teams | Joint physical-cyber incident coordination |
| Device monitoring is limited to uptime or alarms | Device health, configuration, and compliance are tracked centrally |
| Reactive responses to events | Predictive analytics and proactive threat mitigation |

A centralized security dashboard enables layered defense by continuously monitoring device health, detecting misconfigurations, and flagging outdated firmware in real time. (source)
Properly implement incident response and recovery in converged environments
An incident today rarely respects boundaries, which is why incident response must be coordinated across physical and cyber teams. A cyber breach impacting badge systems may require physical lockdowns, for example, or a breached gate may necessitate a forensic review of network access logs. Response plans must include hybrid scenarios where attackers shift tactics, moving from digital intrusion to physical manipulation or vice versa.
Incident playbooks should specify escalation criteria, communication paths between security operations centers (SOC) and facility teams, and predefined action sequences for operational shutdown and recovery. Drills and simulations are a necessity and the only way to validate that personnel can navigate blended crises under pressure.
For example, during a cross-domain incident simulation at a regional airport, a cyber intrusion targeting badge access systems was paired with a physical intrusion at a secured maintenance hangar. The exercise revealed gaps in coordination between IT and physical security teams, specifically, delays in sharing logs and uncertainty about escalation procedures. Lessons from the drill were used to update the playbook and implement a joint communication protocol.
Build a security-first culture
Technology alone cannot defend a system; it must be supported by a workforce that understands its role in protection. Security-first culture begins with getting buy-in from the organization’s leadership team. It’s also necessary to cross-train staff, ensure that physical security personnel grasp basic cyber hygiene, and check that OT engineers recognize the risks associated with unsecured interfaces or default credentials.
Awareness programs must go beyond policy reminders and emphasize real-world consequences, such as how a missed procedure or unauthorized shortcut can enable cascading failures. Governance and accountability frameworks need to ensure that ownership is explicit in every system; whether it’s a camera or a PLC, it must have a defined security custodian. Visibility into asset status, access logs, and anomaly alerts ensures that no critical event is dismissed as routine noise.
Take advantage of automation and remote monitoring
Operational environments are too complex to secure through manual oversight alone. Automation enables continuous monitoring, triggering alerts from physical sensors and network telemetry. Predictive analytics and AI, when applied correctly, can identify deviations such as unusual access patterns or control logic anomalies before they escalate. Remote remediation capabilities, though powerful, require strict control to ensure they do not become a backdoor for adversaries. Automated systems must enhance, but not replace, human judgment. They serve as force multipliers, allowing security teams to act before an incident becomes unrecoverable.
For example, a logistics company managing multiple distribution centers integrated its video surveillance, access control, and alarm systems into a single dashboard. This reduced false alarms by 60% and helped operators respond more quickly to genuine threats, especially during off-hours when coverage was limited.
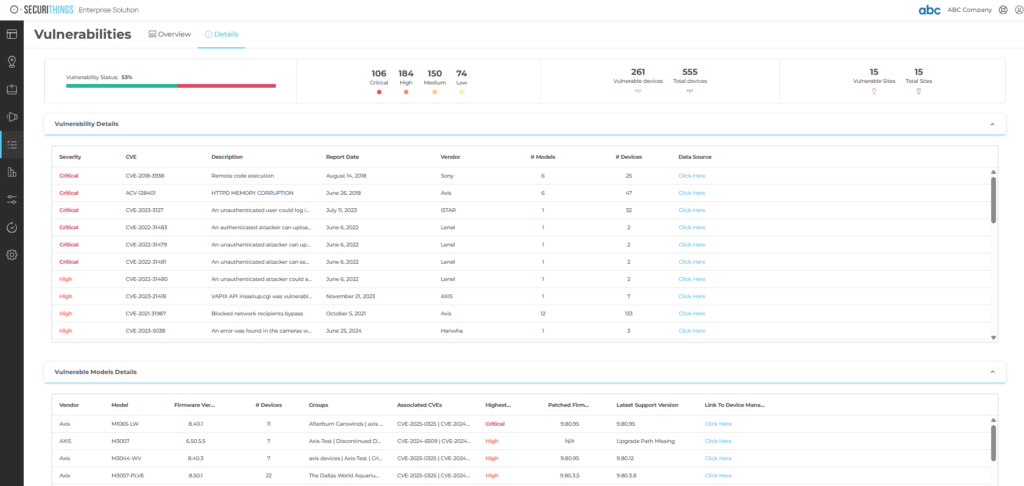
Automated security platforms support real-time monitoring and alerting across physical and digital layers, enabling faster response to device anomalies and access violations. (source)
Check third-party and supply chain security
Every component introduced into a physical or cyber ecosystem carries inherited risk. Vendor systems with remote access, contractor devices connecting to internal networks, and externally maintained equipment must all be managed under strict verification. Supply chain hardening requires more than procurement checks; it involves lifecycle oversight, patch verification, firmware validation, and contractually defined security responsibilities. Shared responsibility must be explicit and vendors must adhere to the same controls and monitoring standards as internal teams. A single compromised hardware component or unvetted integration can undermine all other defenses.
Institute a continuous improvement plan for future readiness
Security in critical infrastructure cannot remain static: Regular testing and auditing of both physical and cyber controls reveal weaknesses before adversaries do. Integrating threat intelligence allows organizations to adapt based on emerging attack trends, whether it is AI-driven reconnaissance or targeted ICS malware.
Future-focused security must recognize that the threat landscape will continue to become more complex, as adversaries explore convergence points that no current policy has yet addressed. Resilience depends on an ongoing cycle of improvement which includes reviewing, testing, fortifying, and evolving.
The future of physical security and cybersecurity
The future of physical and cybersecurity will be shaped not just by convergence, which is already underway, but by how organizations automate, predict, and adapt to a constantly shifting threat landscape.
One major shift will be the rise of AI-driven threat activity. Adversaries are increasingly using AI to automate reconnaissance, craft convincing social engineering attacks (including deepfakes), and probe for vulnerabilities in both physical and digital systems. In parallel, defenders will rely on AI to detect abnormal behavior, correlate physical and cyber signals, and even initiate autonomous remediation before a human response is triggered.
5G and edge computing will also expand the attack surface. Physical security devices, from smart locks to cameras, will increasingly process and transmit data in real time, often outside traditional network perimeters. This shift will require new policy models, including zero trust enforcement at the edge, device-level encryption, and continuous authentication.
Another key trend is the emergence of Converged Security Operations Centers (C-SOCs). These facilities unify cyber and physical telemetry to produce a more complete threat picture. For example, if a badge reader logs abnormal access at the same time as suspicious network activity, a C-SOC can correlate those signals and respond faster than separate teams operating in silos.
Future-facing organizations will also invest in cryptographic provenance for hardware and access control devices, verifying the integrity and origin of components to prevent tampering or counterfeit deployment in the field.
Finally, adaptive policy frameworks will replace static documents. These will be backed by real-time metrics such as device uptime, alert fatigue rates, and average response times. Platforms that integrate policy execution with monitoring and analytics will allow organizations to shift from compliance-driven security to intelligence-driven security.
Conclusion
The convergence of physical security and cybersecurity is the operational reality of modern critical infrastructure. The risks you face do not respect domain boundaries, so neither can your defenses. A breach today may begin with a wire and end in a network, or start in code and manifest as a catastrophic physical outcome. Treating security as a collection of disconnected functions is no longer viable.
True resilience demands a holistic mindset, one where protecting people, facilities, data, and systems is approached as a single, unified mission. The physical and cyber domains are inherently interconnected, each capable of exposing the other if left uncoordinated. Security must therefore be built on collaboration across disciplines, where engineers, operators, and cybersecurity teams share visibility, intelligence, and accountability.
This is more than an operational adjustment; it is a strategic imperative. Organizations cannot afford to be reactive or siloed. They must take proactive steps to integrate governance, align incident response, and invest in joint capabilities, including platforms that unify physical and cybersecurity operations and anticipate threats instead of merely responding to them. Those who embrace this future will move beyond protection toward proper anticipatory defense equipped to confront threats that respect no boundary between the physical world and the digital realm.