Physical Security Assessment Best Practices
- Chapter 1: Tutorial & Best Practices
- Chapter 2: Commercial Building Security Systems
- Chapter 3: Physical Security Systems
- Chapter 4: Data Center Physical Security
- Chapter 5: Physical Security Cybersecurity
- Chapter 6: Physical Security Plan
- Chapter 7: Physical Security Controls
- Chapter 8: Retail Security Systems
- Chapter 9: Physical Security Tools
- Chapter 10: Physical Security Program Best Practices
- Chapter 11: Physical Security Policy Best Practices
- Chapter 12: Best Practices for Physical Security and Cybersecurity
- Chapter 13: Best Practices for Corporate Physical Security
- Chapter 14: Physical Security Best Practices
- Chapter 15: How physical security powers
- Chapter 15: Best Practices for Physical Security Devices
- Chapter 16: Physical Security Assessment Best Practices
- Chapter 17: Corporate Physical Security Strategy Best Practices
Physical security assessments are a cornerstone of an effective enterprise risk management (ERM) program. Whether assessing physical or cybersecurity vulnerabilities or bridging the gap between both domains, these assessments ensure that underlying threats to people, assets, and operations are properly identified. When audits follow industry-recognized standards, security professionals make it easier to achieve and maintain strong corporate governance compliance.
A holistic physical security assessment provides companies with a clear understanding of their assets, the threat landscape, and the frequency/impact of potential disruptions. Mature programs should validate their findings through real-world testing to better understand if their controls are working effectively. An often-overlooked component of the assessment program is the remediation process; without clear ownership and change management, assessments are of little meaningful use.
This article discusses physical security assessments and outlines best practices for implementing a physical risk assessment framework, developing testing standards, and providing a plan for closing identified gaps.
Summary of key best practices for physical security assessment
| Best practice | Description |
|---|---|
| Implement physical security assessment within the ERM program | Develop a physical security assessment plan as part of the organization’s enterprise risk management program. |
| Use an industry standard threat/risk model as a benchmark | Tailor an industry-recognized methodology as an underlying framework for developing organization-specific assessments. |
| Evaluate security as a holistic, integrated system | Measure how security processes interface together rather than looking at hardware, software, and people in isolation. |
| Conduct real-world testing | Use scenarios, penetration testing, and/or red teaming to identify vulnerabilities, test detection methods, and implement mitigation measures. |
| Implement a remediation program | Develop a framework for addressing identified vulnerabilities. |
-

Monitor the health of physical security devices and receive alerts in real-time
-

Automate firmware upgrades, password rotations & certificate management
-

Generate ad hoc and scheduled compliance reports
Implement physical security assessment within the ERM program
Physical security assessments should be a core pillar of an organization’s ERM program. These assessments help position the security program as a strategic partner, shifting security from a cost center to a business enabler.
Risk management vs. risk assessment
Security teams can fall into a trap of conducting security assessments without translating their findings into concrete actions. Before implementing expensive technical controls or exhaustive procedural controls, security practitioners need to understand the difference between the two concepts:
- Risk management: The governance and decision-making apparatus of prioritizing mitigation based on budget, culture, compliance, and business needs.
- Risk assessment: The framework and diagnostic process of identifying vulnerabilities, likelihood, and potential impact.

A holistic understanding of risk management and risk assessment requires communication between both parties. (source)
As part of the process of risk management compliance, security teams might be tasked with ensuring that their physical infrastructure is hardened against cyber threats. A risk assessment reveals that, due to multiple systems and distributed technologies, there are gaps in configuration and patch management. The security program then institutes a continuous monitoring system to automate device management to close the identified vulnerability.
Select the appropriate risk assessment for the organization
Different organizational risks require different assessment types. Security teams should consider what approaches best address their assets, their vulnerabilities, and the scope/remit of their programs.
| Assessment Type | Key question |
|---|---|
| Physical Security | How are the security systems designed, and do they integrate with operational procedures? |
| Cybersecurity | What are the organization’s policies on zero trust and data protection? |
| Insider Threat | What measures are in place to monitor those with higher levels of access or deviations in behavior? |
| Hybrid/Converged | What is the organization’s security culture and 3rd party vendor management? |
Internal vs. external auditors
One of the most common questions that security teams face is “Who should conduct the security assessment?” The right answer depends on organizational needs, internal practitioners’ capability/expertise, and the perceived independence required for audit findings.
A practical hybrid approach could be the best method: Internal practitioners conduct regular assessments while external specialists perform periodic deep-dives and specialized assessments to provide an objective view that validates controls and benchmarks against industry best practices standards.
Use an industry standard threat/risk model as a benchmark
Industry standard threat/risk models provide a structured, validated, and (if required) repeatable method for physical security assessments. The most effective approach is for practitioners to adapt these methodologies into their own customized frameworks that reflect their companies’ business needs, operating environments, threat landscapes, and risk tolerance levels.
Risk assessment frameworks
The table below lays out four widely recognized frameworks that offer different strengths depending on organizational needs and assessment objectives. While not universally applicable to all organizations, these frameworks can help provide a starting point for customized development.
| Framework | Best suited for | Strengths |
|---|---|---|
| CARVER (US Military) | Critical infrastructure, defense companies, public venues/government |
|
| RSA (Risk Assessment Standard – ASIS) | Enterprise corporations across industries |
|
| 31000 Risk Management (ISO) | Global organizations seeking compliance and regulatory credentialing |
|
| Cybersecurity Framework (NIST) | Enterprise corporations across industries |
|
No single framework, out of the box, will likely address a company’s unique security threats, needs, and environment perfectly. For example, a data center operator headquartered in the United States but also operating in Europe might need to consider a mix-and-match approach of Carver (due to their role as a critical infrastructure operator) and ISO (as a global organization) standards.
Build a hybrid framework tailored to your organization
Standardized frameworks provide an overall structure but should be tailored to meet the organization’s needs. Here are some high-level questions to consider in the customization process:
- What framework should be used? Select one that aligns as closely as possible with the industry, meets any regulatory/compliance requirements, and is recognized by the organization’s key stakeholders.
- Are there company-specific requirements? These can be interdependencies, assets, and/or emerging threats that need to be reviewed.
- Which threats are being assessed? This can include physical, cyber, reputational, insider, and converged risks.
- What are the assessment criteria? This is based on the organization’s operating environment, risk tolerance, and business priorities.
- Should stakeholders be included? This reflects the fact that the model most accurately assesses what is important to the business.
For example, a biotechnology company might use the ASIS RSA as its foundation and then add custom assessment criteria for reputational risk when bringing a new drug to market, given the potential concerns about excessive pricing.
Use scenario-based testing to assess controls
Security assessments become more meaningful when they are stress-tested against realistic, likely threats that an organization might encounter. Security practitioners should consider the following as an example of how to think about scenario testing.
Scenario: Ransomware attack targets physical security infrastructure of a financial services firm
- An attacker gains network access and deploys ransomware that encrypts and disables multiple physical security systems.
- Employees cannot badge into administrative sites; visitor management systems are disabled.
- Banks lose access to video management systems; local and centralized alarm systems are offline.
- ATMs lose remote monitoring systems.
Assessment Questions:
| Assessment question | What it does |
|---|---|
| Is the firm susceptible to insider threats or phishing attacks? | Provides insight into company culture and procedures |
| Does the firm have a holistic system to determine the operational status of each system/device/technology? | Measures automation and response time to outages |
| Does the access control system behave differently for administrative sites (fail-safe) versus banks (fail-secure)? | Validates how specific technologies are configured for operational use |
| Do administrative and banking employees have continuity procedures, and are they routinely exercised? | Determines whether personnel know procedures |
| How are ATMs treated from an operational and continuity standpoint? | Determines if technologies are configured for specific assets |
| Are backups of the security systems routinely made and regularly tested? | Validates whether systems are regularly tested |
| What are the recovery time objective (RTO) and recovery point objective (RPO)? | Considers how events impact financial or reputational management. |
This type of scenario-based testing exposes gaps that traditional checklists might miss, particularly vulnerabilities at the intersection of physical and cybersecurity. Device management systems play an essential role in this context by maintaining current inventories, configuration baselines, and firmware status across all physical security infrastructure, enabling faster recovery.
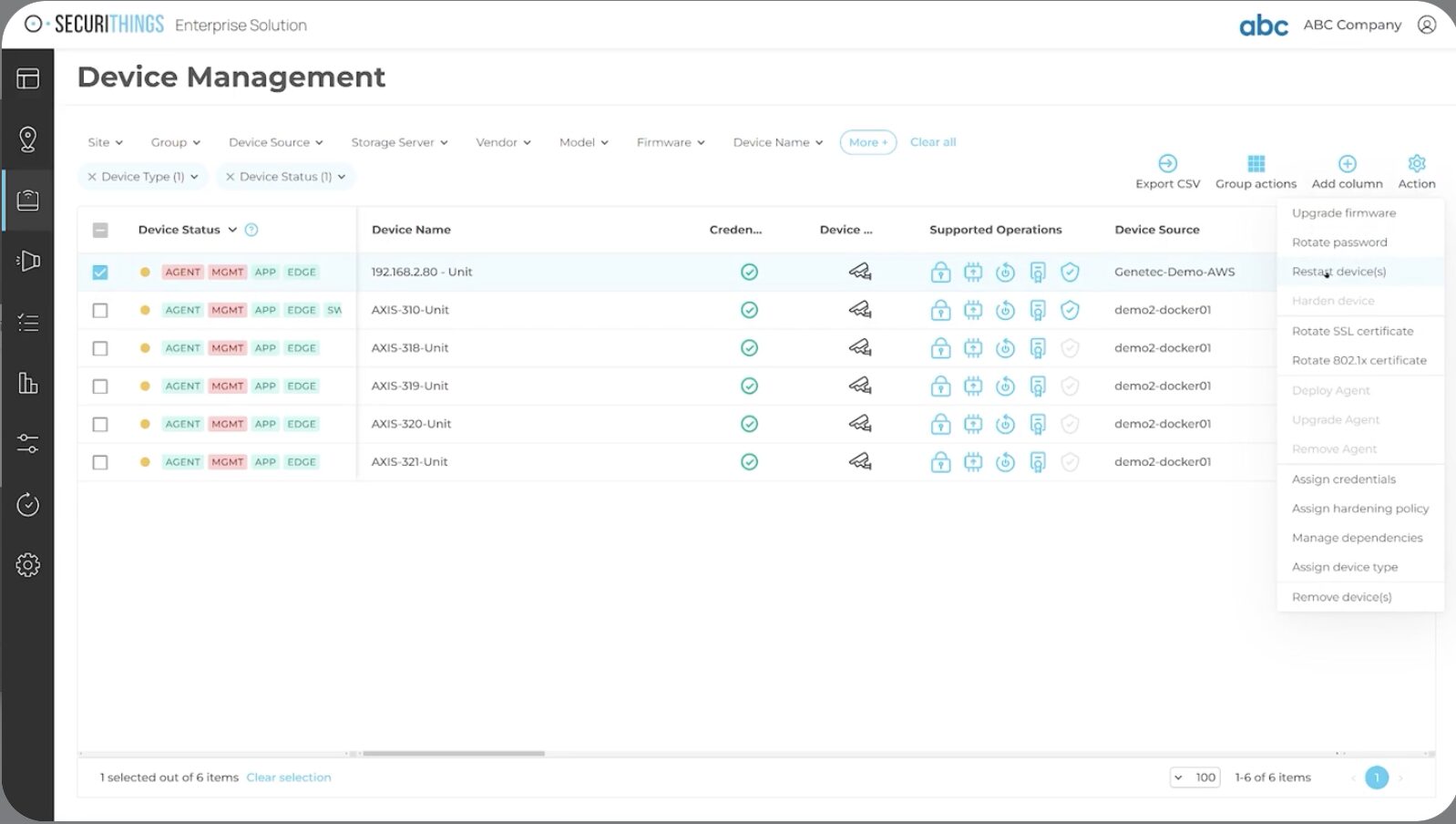
Device management is essential in managing vulnerabilities against complex infrastructure systems. (source)
Deploy cloud-based assessment checklists
Cloud-based platforms are transforming how corporate security teams conduct, document, and access their security assessments. Mobile-optimized platforms give assessors real-time access, version control to track revisions, and image capture and upload capabilities. These systems can also provide trend analysis, pattern recognition, and link directly to the remediation plan.
Organizations transitioning from paper to cloud-based deployment should use a phased approach to ensure data integrity and minimize data loss. This process should include ensuring standardized workflows, conducting testing of data processing, and implementing a staggered approach to migration.
Evaluate the security program as a holistic, integrated system
Security assessments often evaluate individual components—whether technology, personnel, or procedures—in isolation. Assessments should take a more holistic approach, identifying critical vulnerabilities where systems intersect.
Assess control types in both the physical and cyber domains
Security controls should be assessed across both physical security and cybersecurity. An essential component for any assessor is to understand the relationship, interdependencies, and department culture (if under separate functions) to assess how they might function during an incident.
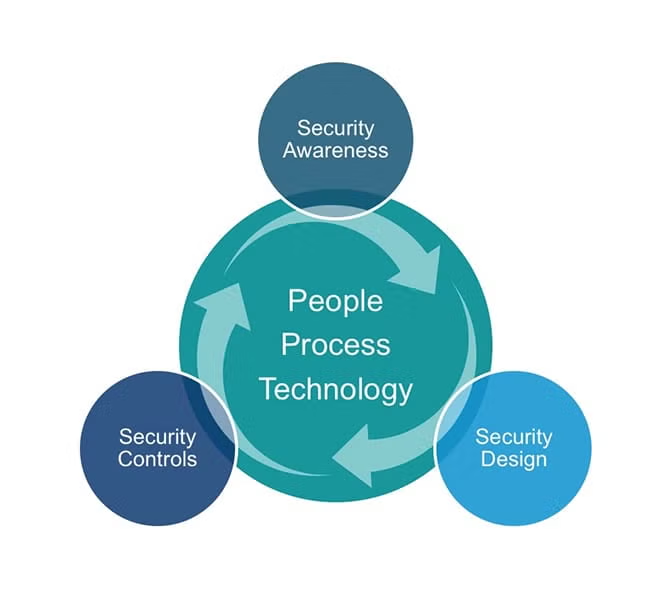
Assessing security controls involves understanding how people, processes, and technology work together. (source)
| Control Type | Function | Key Question |
|---|---|---|
| Directive | Policies, procedures, and training | Are employees trained to recognize, respond, and continue operating during an incident? |
| Preventive | Hardware or software to minimize the likelihood of an incident | Are systems, rules, and provisioning designed to deter, identify, and isolate physical/cyber intruders? |
| Detective | Hardware or software to determine when an incident is occurring | Does our technology provide real-time alerts to physical/cyber anomalies? |
| Corrective | Systems to respond to an incident occurring | Do we have a unified approach for managing incidents? |
Implement vendor reviews of KPI/SLA as part of the assessment process
Key performance indicators (KPIs) and service level agreements (SLAs) provide objective data on how well interconnected processes actually perform. As part of the assessment process, assessors should deep dive into vendor data and ask some of the following questions to determine whether there are integration gaps between systems, people, and processes.
Security system KPIs:
- Device uptime and availability: What percentage of security systems remain operational during a disruption? Do outages cluster in specific locations or system types?
- Mean time to detect (MTTD) and mean time to respond (MTTR): How quickly are security incidents identified and remediated? If delays occur, where are they in a process, e.g., detection, notification, or response?
- Integration health: Are individual security systems configured to notify the security operations center if there is an operational outage? Does the organization need automated device management for managing large-scale physical security infrastructure?
- Configuration consistency: Do devices across the infrastructure maintain standardized security settings, or has misconfiguration created vulnerabilities?
Personnel KPIs:
- Turnover: What is an acceptable level of security personnel attrition per year?
- Technical skills: Are security personnel trained and capable of solving basic outages, or do all technical issues need to be routinely escalated to vendors?
- Procedural compliance: Are manual backup processes tested regularly and proven effective?
Vendor SLA performance:
- Response time: In the event of an outage or system disruption, do security integrators and guard force providers meet contractual obligations for system repairs, technical support, and personnel continuity?
- Remediation quality: Are issues resolved permanently, or do the same problems recur?
Conduct real-world testing
Physical security assessments remain theoretical unless practical exercises are undertaken to stress-test them under real-world conditions. Assessments that model likely events move testing from the theoretical to the practical, exposing gaps, validating controls, and better informing stakeholders on the process.
Selecting an appropriate testing methodology
Security teams should consider their threat environment, risk tolerance, involvement of stakeholders/business leaders, and the potential for business disruption when selecting an appropriate testing criterion.
| Approach | Scope | Key concept | Best for understanding |
|---|---|---|---|
| Scenario | Table exercise with stakeholders modeling an event | Controlled environment with step-by-step prompting | Organizations determining their baseline capabilities.
Do we have a business continuity plan? |
| Penetration testing | Focused assessment of a location, system, and/or process | Specific testing against known or likely vulnerabilities | Organizations testing known vulnerabilities with clear objectives.
Can an attacker bypass our physical access controls? |
| Red teaming | Multi-pronged assessment testing multiple controls | Unrestricted attack methods | Organizations testing threat actors employing any attack methods.
How would an attacker enter our facility, steal our product, and leave undetected? |
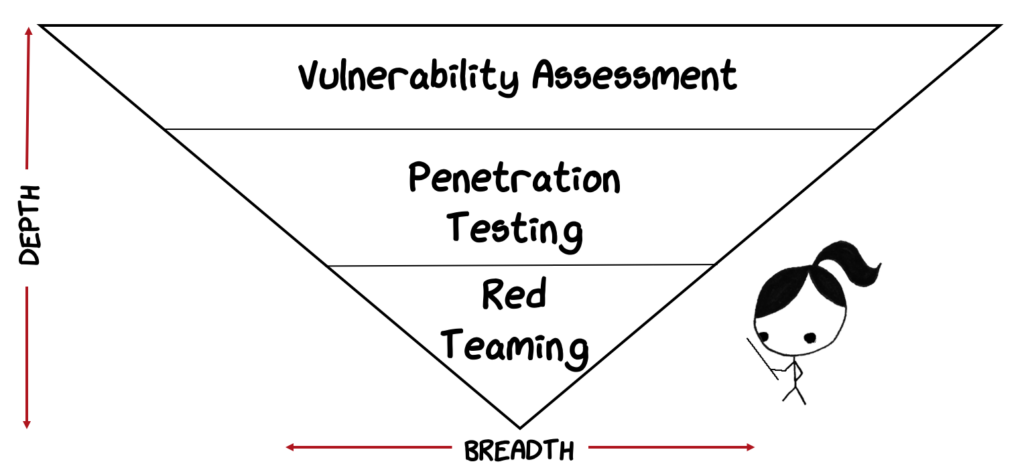
Depth versus the breadth is a key differentiator when selecting a testing methodology. (source)
Establish clear scope and rules of engagement
An effective testing exercise requires that practitioners establish and adhere to a defined scope and clear rules of engagement for consistent, verifiable, and validated sampling. Here are some areas to look at:
- Executive buy-in: Ensure that executive stakeholders are made aware of the perimeters of the testing and have agreed to participate.
- Define objectives and boundaries: Determine what systems, processes, and personnel are within the scope of the assessors to target.
- Information gathering phase: Determine the level of pre-operational intelligence to provide the assessors.
- Reconnaissance phase: Determine the level of active reconnaissance (e.g., scanning the network or conducting phishing on employees) that the assessors will be permitted to exercise during the test.
- Execution phase: Active testing of the security program to capture data, processes, and the current mitigation measures. Implement an escalation process for how real-world incidents are handled during testing to avoid coverage gaps.
- Documentation phase: Determine what content is needed for the final report, examples of vulnerabilities discovered, methodology used for security practices, and needed remediation gaps..
Implement a remediation plan
A remediation program is a formal component of an established (ERM) program. This program should not be an ad hoc response to security assessment findings but should establish clear ownership of risks, mitigation measures to prioritize, and formal timelines.
Security practitioners should provide their risk owners with an itemized and catalogued risk register. This risk register should be linked to the assessments and provide details such as risk category, impact, likelihood, and risk owner. It is a best practice to make the information as easily digestible and understandable as possible to help with risk management implementation.
As part of this process, security teams should collaborate with their stakeholders on the development and prioritization of a plan, which should include strategic questions in the following areas to start:
- Risk-based approach: Which vulnerabilities pose the highest likelihood/impact to critical operations?
- Quick wins: What steps can be taken immediately to close gaps (often overlooked but important)?
- Long-term planning: What mitigations can be addressed with simple procedural changes and/or limited budget versus long-term operational changes or capital investment?
- Cultural changes: Will new/enhanced security practices disrupt workflow, or do they require significant behavioral buy-in from employees?
An overlooked consideration is the importance of an executive briefing, showcasing to leadership that corporate security and risk owners are in the process of closing identified gaps.
Last thoughts
Physical security assessments provide a structured process for identifying and correcting organizational vulnerabilities. As part of an enterprise risk management program, assessments can ensure that companies remain compliant, validate their controls, and are prepared to mitigate their vulnerabilities.
When you evaluate systems, people, technology, and processes holistically, your organization is much better equipped to mitigate risk. To get the most out of the assessment, security teams should use a centralized management platform. This platform gives them the clear visibility needed across their physical security infrastructure to spot gaps and manage risks.